Figure 3
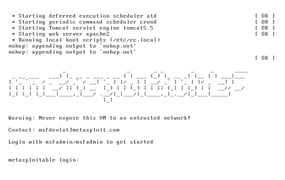
Figure 3: Metasploitable, an extremely vulnerable version of Linux, offers good attack vectors.
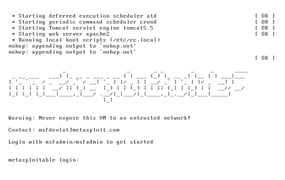
Figure 3: Metasploitable, an extremely vulnerable version of Linux, offers good attack vectors.