Figure 2
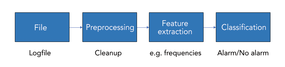
Figure 2: Processing steps in supervised learning.
Figure 2: Processing steps in supervised learning.